We will show you how to deploy Docker image from private repository to you cluster 1. Default space for obtaining images is Dockerhub which doesn't require:
- neither repository address specification, i.e. images are pullable as
docker pull redis, - nor any login - i.e. "just pull it as it is",
and therefore is a good demostration since everybody is familiar with it.
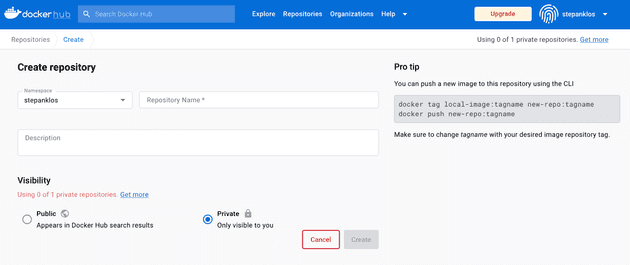
We show how to use your 1 free private image hosting slot on Dockerhub for your private image.
1. Create Private repository + populate it
Create 1 free Private repository for your project on docker hub.
Build your project in project's folder (cd ~/projects/project-folder) and push it as
docker build -t stepanklos/private-image .
docker login
docker push stepanklos/private-image2. Prepare login mechanism for Kubernetes-Dockerhub
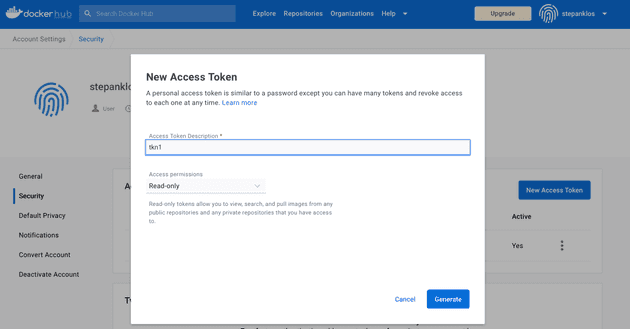
To pull from private repository, you first need to be authenticated with Dockerhub. To achieve that, you either can use pair e-mail/password, which is obviously giving you access over whole Dockerhub account with all privileges. You can also create something called Access Token 2 for performing specific restricted operations as e-mail/token in order to store it as Kubernetes Secret 3 and use it for authentication while pulling in Deployment.
Generate Access Token
Please navigate to Security section in your Account Settings and click New Access Token. Select READ only and copy the provided token.
Prepare Kubernetes Secret
Create JSON with authentication token. Provided token should be placed into password and serves as a "password for user with restricted righs".
dockerhub-cred-pull.json
{
"auths": {
"https://index.docker.io/v1/": {
"username": "stepanklos",
"password": "dckr_pat_a2l7yEhuBBHsNntBC6wK7NEV5EA"
}
}
}Create Kubernetes Secret from dockerhub-cred-pull.json in your Cluster.
kubectl create secret generic dockerhub-cred-pull \
--from-file=.dockerconfigjson=/Users/you/projects/app/dockerhub-cred-pull.json \
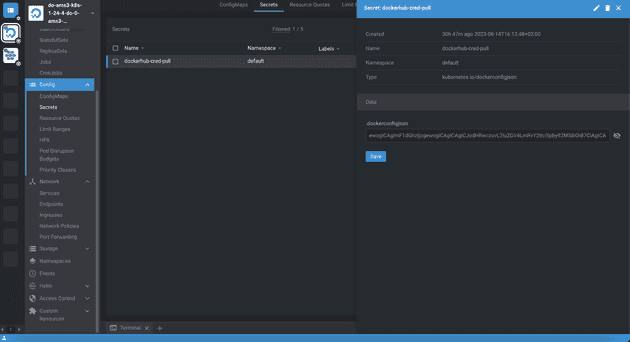
--type=kubernetes.io/dockerconfigjsonVerify whether your Secret was created successfully.
kubectl get secret dockerhub-cred-pull
kubectl get secret dockerhub-cred-pull --output=yaml
kubectl get secret dockerhub-cred-pull -o jsonpath='{.data.*}' | base64 -dAlternatively, view Secret in Lens. Clicking the diagonally striked eye symbol will perform decoding json from base64 for readability purposes.
3. Deploy using authentication via. Access Token
You will have to add this snippet at the end of your Deployment.
imagePullSecrets:
- name: dockerhub-cred-pullThis snipped should be nested in spec: > template: > spec > containers: | imagePullSecrets:, i.e. "on the same level as containers specification".